Log4Shell Vulnerability Exploited to Plant the Khonsari Ransomware

The recently discovered security hole in the Log4j service has quickly attracted attention from cybercriminals specializing in various types of attacks. Although initial reports mentioned mostly botnets and cryptocurrency miners, it seems that ransomware operators are also on the prowl for servers exploitable through the Log4Shell vulnerability. Thanks to this exploit, criminals gain the ability to execute remote commands on the compromised systems, effectively enabling them to perform all sorts of tasks – such as to run the novel Khonsari Ransomware.
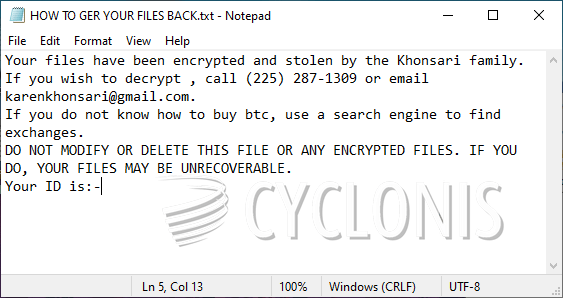
Khonsari Ransomware Operators Use a Phone Number for Contact
The Khonsari Ransomware is not related to any of the file-locker families that came out in 2021, and it appears to be a very new piece of software. Unfortunately, initial analysis of the payload shows that it uses a flawless file-encryption mechanism, which would make it impossible to develop and release a free decryptor. This leaves victims of the Khonsari Ransomware with very limited options when it comes to recovering their files.
It is important to add that the Khonsari Ransomware was not seen until the Log4Shell vulnerability was disclosed. So far, this seems the only method that its creators are using to infect systems. The malware is able to swiftly encrypt a large portion of the victim's files, and append the suffix '.khonsari' to their name. Just like other file-lockers, this one also opts to show a ransom note after completing the attack.
The criminals of the Khonsari Ransomware ask their victim to pay a ransom fee via Bitcoin, and to contact karenkhonsari@gmail.com for additional information. The surprising thing in their ransom message is the presence of a phone number, which can be used to reach them – (225) 287-1309. It is advisable not to agree to send money to anonymous cybercriminals. If you pay, you might not get anything in return, losing both your money and your files. It is best to remove the Khonsari Ransomware via antivirus software, and then explore alternative data recovery options. Of course, make sure to also update your Log4j service in order to fix the vulnerability.








