Threats

Nearly 70% of Spam Comes from Russia, Ukraine, Germany and the U.S., New Study Finds
We’ve all been exposed to spam. In some cases, it can reach us via text messages we receive on our mobile devices. In other cases, the schemers behind the misleading messages can operate via social networking... Read more

8 Android Security Tips That Will Help You Manage Your Own Security
Android mobile phones and other devices are both well-known and popular among many users. In this blog post, we talk about Android security as well as provide security tips for Android users. We highly recommend... Read more

Cyber Security Is Not a Luxury, and Password Management Does Not Need to Cost You a Fortune
Some users do not think there is any point in trying to protect their cyber security because they believe that the only way to do it is by purchasing expensive tools. However, it is entirely untrue. There are lots of... Read more

What Is Retadup and How Can It Jeopardize the Security of Your Passwords?
Retadup is one of the malware families that has never really managed to catch the attention of mainstream media the way Trickbot has, for example. This seems a bit strange because while it has never really been the... Read more

What Hackers Do After Gaining Access to a Website
What are Hackers' objectives? Hackers usually infect websites with malware. Malware can execute many complex and malicious actions on a website, such as malvertising, illegal downloads, ransomware, and more. Online... Read more

WhatsApp Spyware Update: It Can Now Steal Your Data from Facebook, Microsoft, Amazon, Google, and Apple
Our mobile phones and computers store lots of personal and sensitive information, and it is not a secret that nowadays cybercriminals are incredibly interested in stealing such data. Thus, the need to secure data... Read more

Meet Smominru, a Dangerous Malware That Could Try to Steal Your Credentials
You could say that the Smominru worm isn't the most widely known cyber threat out there. It has indeed attracted some attention, mostly from cybersecurity experts, but overall, it hasn't been mentioned in the news as... Read more

Let InnfiRAT In, and Your Passwords and Crypto Wallet Data May Be Stolen
You might think that stealing people's money over the internet isn't that hard. You just compromise some credit card details or some online banking credentials, and you're ready to go. The thing is, it's a bit more... Read more
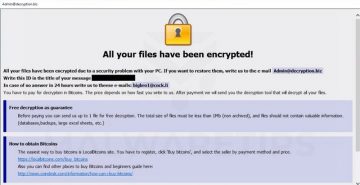
Want to Survive Ransomware - Here's How to Protect Your PC
IT security experts have argued that “ransomware is everything bad about humanity distilled into malware—maliciousness, greed, and casual incompetence”. It’s not difficult to see why some of them could hold that... Read more

Signs Your Phone Has Been Infected With Stalkerware and How to Get Rid of It
There are all kinds of malware out there these days, and while a lot of them can cause you significant inconvenience, damage, and even financial losses, there's something about stalkerware that's extra disturbing. The... Read more

What Is a DDoS Attack and How to Avoid It
Directed denial of Service, or simply "DDoS" attacks, are designed to take down a platform or web page and interrupt the service it provides. This temporary loss of service is caused by overloading a single website... Read more

Going Back to School? Consider Using a VPN
If you just got accepted into college, you might be concerned with things like finding a place to live or getting to know your classmates. However, specialists urge to think about cybersecurity in college too. One of... Read more

If a Bank Sends You Your Passwords via a Text Message, This Android Trojan Could Steal Them
Do you still think that a successful malware operation depends on talented hackers creating a bespoke piece of malware that can keep security researchers and law enforcement agencies off the scent? You might want to... Read more

The Hackers Behind the Gootkit Malware Forgot to Secure Their Database with a Password
Some people have problems getting their heads around how much damage a cybercrime operation can do. ZDNet's Catalin Cimpanu and SecurityDiscovery.com's Bob Diachenko spent some time looking closely into an... Read more

5 Continuously Growing Cyberthreats You Should Watch Out For
The online world is not a safe place, but how dangerous is it exactly? Read the news on a website dedicated to cybersecurity, and you'll be left with the impression that more or less every link you click on and every... Read more

Canon DSLR Hacked With Crypto-demanding Ransomware – but for Research
Technology is a marvelous thing, and the Internet has made a reality out of a multitude of things that were thought impossible just a few years back. Information on any topic imaginable is at the tip of a user's... Read more

Keep Your Info Safe: Now Is the Time to Know Emerging Cyber Threats
Because of the ever-expanding spread of digital technologies across the world, authorities must hasten the modernization of law enforcement agencies in addition to building an integrated cybercrime management... Read more

What Is Formjacking and How to Protect Your Passwords Against It?
Which are the two types of cyberattacks that are most frequently mentioned in the news? The first one that has probably crossed your mind is ransomware, and this is hardly surprising. Quite apart from the fact that... Read more