Threats
LockerGoga Aims to Attack Critical Infrastructures Worldwide by Joining Efforts as Part of a Ransomware Trio
Investigators say that LockerGoga, MegaCortex, and Ryuk ransomware are used in attacks, targeting critical infrastructures across the world. Ransomware has been causing serious chaos in businesses all over the world.... Read more

Security Experts Warn That Victims of Ransomware Attacks MUST Change All Passwords
When an organization is hit by ransomware, many people tend to think that the only thing to worry about is restoring the data as quickly as possible. Earlier this week, however, cybersecurity reporter Brian Krebs told... Read more

What Is a Deepfake and How Can It Affect Our Cybersecurity?
We're now closing in on the end of the year, which means that it's time for cybersecurity experts to start jotting down their predictions for 2020. You can be pretty sure that they'll try to warn people about all the... Read more
Let's Bust 10 Myths That Android and iPhone Users Continue to Believe
How important is your smartphone for you? Do you keep up with your business endeavors using it? Do you mainly use it to communicate with your family and friends? Perhaps it’s a tool for entertainment? Whatever the... Read more
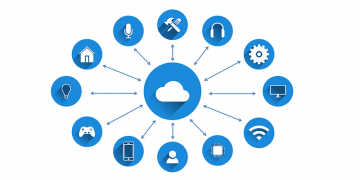
5 Security Tips That Will Help You Protect Your IoT Devices
There’s a dark side to anything popular. Anything that grows eventually has to face a number of threats trying to bring it down or exploit it. It seems that the Internet of Things is becoming the next best thing in... Read more

Macy's Customers Start Receiving Information on How to Protect Their Accounts After a Data Breach
Surveys suggest that according to users, businesses are responsible for protecting people's personal information and should take all the responsibility after they suffer a data breach. Sometimes, however, things... Read more

Emotet Malware Attacks Governments and Organizations Costing Victims Millions
Emotet is arguably the most problematic and costly malware of the past five years. This malware was first discovered in 2014, and since then, it has been causing trouble almost non-stop. The threat took a sort,... Read more

Ransomware Operators Can Now Steal Your Data Before Encrypting It
Ransomware has proven time and again to be one of the most powerful weapons in the cybercriminals' arsenal. Initially, hackers would need to create their own family of file-encrypting malware, which isn't exactly a... Read more

Workstations in a European Airport Found to Be Riddled with Crypto-Miners
When you walk into an airport, you might expect crowds, overworked staff, people who had too much fun with the free perfume samples at a duty-free store, and bad food. And you might be willing to accept it all. It’s... Read more

Students of an Ivy League University Are Bombarded with Fake Job Offers via Phishing Emails
Are you a Dartmouth student? Are you ready to start a career linked to your degree? If you are, you need to look out for phishing emails that might offer high-paying jobs. It is possible that the schemers behind these... Read more

Attention: Schemers Use the Accounts of Your LinkedIn Contacts to Send You Phishing Messages
You probably already know that you should never interact with messages that come from unknown senders, but what do you do when someone from your contacts sends you a link or a file and asks to view it? If you want to... Read more

Facebook “Verified Page” Scam Alert
If you still don’t have a Facebook account, it’s hard to say what you’ve been doing with your life so far. The humongous social networking website has grown into something far bigger than just a medium to broadcast... Read more

The Most Surprising Cyber Hacks That Shook Us in 2019
Cyber security threats kept growing in 2019, and it is expected that they will continue to increase in 2020, despite all efforts to stop it. Every time a weakness is patched, hackers find another system with a... Read more

DeathRansom: Ransomware Hellbent on Killing Files on Infected PCs via Encryption
Ransomware has turned into such a global problem for computer users and businesses, victims of recent threats have turned to budgeting for an attack so they can pay the demanded ransom and get their computer back to... Read more

Hacker Introduces a Lightning Cable That Can Load LockScream to Steal Mac Passwords
Remember when we talked about the potential security threats behind using someone else’s charger? Well, the same developer who revealed a flaw in the Apple security back in August 2018 is now back with fully developed... Read more

Is Your Computer One of the 500,000 That Send out 30,000 Sextortion Emails Every Hour?
You might have received an email claiming that someone has recorded video footage or captured images that, allegedly, can compromise your reputation. This email should state that hackers were able to spy on you via... Read more

7 Tips That Will Make Your 2019 Black Friday and Cyber Monday Shopping Experience Safer
Black Friday and Cyber Monday can offer huge discounts and help you save a lot of money on preparations for the upcoming biggest celebrations of the year. Unfortunately, scammers see it as an excellent opportunity to... Read more

YouTube Users Are Warned About Videos That Sneakily Promotes a Password-Stealing Trojan
In April, security researchers from Fortinet talked about an ongoing campaign that was spreading an information-stealing malware called Predator the Thief. The campaign in question had been active since at least July... Read more