The Dangerous Power Behind Waqa Ransomware

In the digital age, cyber threats like WAQA ransomware pose significant challenges to individuals and organizations. Understanding the nature of this threat and implementing proactive measures is essential for safeguarding valuable data and maintaining cyber resilience.
Table of Contents
Anatomy of WAQA Ransomware
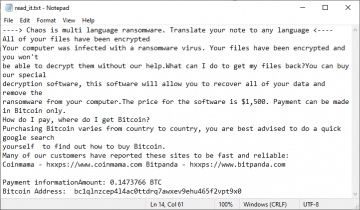
WAQA ransomware emerges as a formidable variant within the STOP/DJVU ransomware family (other versions include Agpo and Zpww Ransomware), distinguished by its aggressive encryption techniques and ransom demands. This malicious software encrypts many personal files, including documents, images, and videos, leaving them inaccessible to users. A distinct marker of WAQA ransomware infection is the addition of the ".WAQA" file extension to encrypted files, as a grim reminder of the intrusion. Victims are then confronted with a ransom note, "_readme.txt," outlining payment instructions in Bitcoin for the decryption key necessary to regain access to their files. The rise of WAQA ransomware underscores the evolving landscape of cyber threats, emphasizing the critical need for robust cybersecurity practices.
Understanding the Ransomware Entry Points
WAQA ransomware employs various tactics to infiltrate systems, exploiting vulnerabilities and user behaviors. Phishing emails, leveraging social engineering techniques, remain a primary vector for malware distribution. Additionally, malicious downloads, compromised websites, and malvertising campaigns serve as conduits for WAQA ransomware propagation. Exploiting weak Remote Desktop Protocol (RDP) passwords provides cybercriminals with direct access to networks, facilitating the spread of the ransomware. Awareness of these infiltration methods is crucial for fortifying defenses and mitigating the risk of infection.
The Encryption Mechanism
WAQA ransomware initiates a sophisticated encryption process upon infecting a device, targeting specific file types using the AES algorithm. Each file is encrypted with a unique key, rendering the data inaccessible without the corresponding decryption key. The original files are replaced with encrypted counterparts bearing the ".WAQA" extension, symbolizing the impact of ransomware on user data. This meticulous encryption strategy underscores the urgency of proactive defense measures and recovery strategies in combating WAQA ransomware.
Immediate Response Strategies
In the aftermath of a WAQA ransomware attack, swift action is paramount to mitigate further damage. Identifying signs of infection, such as the presence of the ".WAQA" file extension, is crucial for containment efforts. Prioritizing containment, preventing the ransomware's spread, and initiating removal and recovery procedures are essential to safeguard remaining data integrity.
Preventative Measures
Combatting WAQA ransomware demands a multi-layered cybersecurity approach. Implementing robust security measures, maintaining software updates, and fostering awareness is pivotal in mitigating risks. Advanced endpoint protection, multi-factor authentication, and proactive network monitoring bolster defenses against ransomware threats.
Backup Strategies
Regular data backups serve as a potent defense against WAQA ransomware attacks. Implementing a 3-2-1 backup strategy ensures data redundancy and facilitates swift recovery without yielding to ransom demands. Periodic restoration tests verify backup reliability, enhancing data recovery capabilities.
Seeking Professional Assistance
In cases of severe ransomware attacks, seeking professional assistance is advisable. The complexity of modern ransomware warrants sophisticated mitigation and recovery strategies beyond standard solutions. Engaging IT security professionals ensures effective response and minimizes the impact on data and operations.
Fortifying Cyber Resilience Against Ransomware
Proactive defense measures and resilience-building strategies are imperative in the face of evolving ransomware threats like WAQA. Individuals and organizations can effectively mitigate the impact of ransomware attacks by prioritizing cybersecurity, fostering awareness, and embracing collaboration. Together, with continuous vigilance and preparedness, we can stay one step ahead of ransomware criminals and safeguard our digital landscape.