Remove Sspq Ransomware

Ransomware threats are designed to encrypt the majority of the files they find on infected machines and then drop a ransom message that extorts the files' owner for money. The Sspq Ransomware follows this exact plan. It is a file-encryption Trojan based on the infamous STOP/Djvu Ransomware family, and victims of its attack may not have many recovery options to choose from. Unfortunately, the file-encryption algorithm that the Sspq Ransomware uses is not decipherable via free utilities – this means that users may need to resort to alternative data recovery options. Many STOP Ransomware variants have been causing trouble worldwide in the past few years - the Mppq Ransomware and XCSS Ransomware are just two of them.
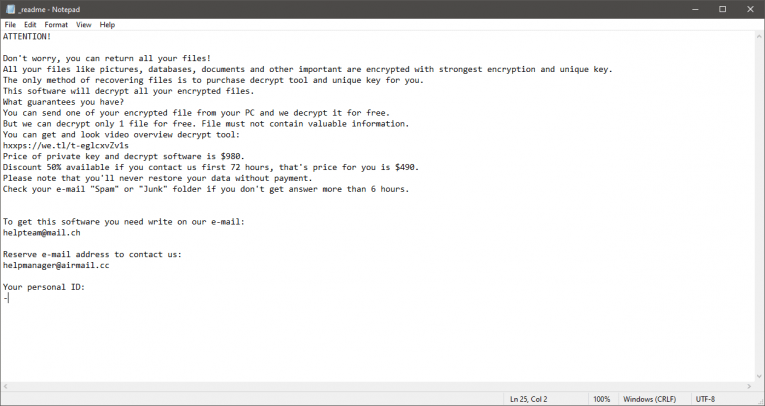
Sspq Ransomware's creators promise to deliver a decryptor to all victims who agree to pay some money via Bitcoin, but we would not advise you to trust them. They ask for a payment of $980, but offer a 50% discount ($490) if the victim pays within three days of the attack. The criminals provide two emails for contact – helpteam@mail.ch and helpmanager@airmail.cc. The full version of their message is stored in the file '_readme.txt' that the Sspq Ransomware drops after the attack.
Files that this ransomware locks are marked with the '.sspq' extension. For example, if you had a file called 'presentation.pptx' it would go by the name 'presentation.pptx.sspq' after the attack. The authors of the malware might be spreading it through malicious email attachments, pirated games/software, fake downloads, misleading ads, or other deceptive content. The best way to stay safe from such attacks is to be careful with the files you download from the Internet, as well as to keep your system protected by a reputable antivirus software suite.
Our advice to victims of the Sspq Ransomware is to disregard the offer of the criminals. Paying them is not a good idea, and you are likely to end up being scammed if you try to co-operate. Instead, run an anti-malware scanner to ensure Sspq Ransomware's removal. After this, try out alternative data restoration tools and options.








