Computer Security

Google Blocks Over 18 Million Coronavirus Phishing Emails on Gmail Each Day
Coronavirus has affected all of us. Living through this pandemic has led to an array of adjustments and a new outlook on social responsibility. Cybercrooks, on the other hand, look at Coronavirus as nothing more than... Read more
Watch out for Fake PayPal SMS Messages That Are Used by Schemers!
It seems that only yesterday we talked about the “New Login From Unknown Device” scam designed to trick unsuspecting PayPal users into giving away their sensitive information. This scam centered around emails that... Read more

How Does the New York SHIELD Act Affect the Privacy of Our Private Data?
Somewhat understandably, the current coronavirus pandemic means that not that many people are thinking about data security at the moment. Nevertheless, the virus will be defeated (hopefully) soon, and we'll need to... Read more
Breach Candy Hospital Leaves 121 Million Patients' Records Exposed
We expect companies that handle our most personal information to take every possible safety precaution to protect us from cybercriminals. However, not all organizations take cyber security seriously even if they are... Read more

Coronavirus Scam Uses a Fake COVID-19 Map Pushing an App That Lets Cybercrooks Spy on You Through Your Phone
We are currently living through a pandemic. Coronavirus is spreading rapidly and has become a global issue. People are scared, and the news is only adding to that fear. Every time you turn on a TV, open a site, or any... Read more
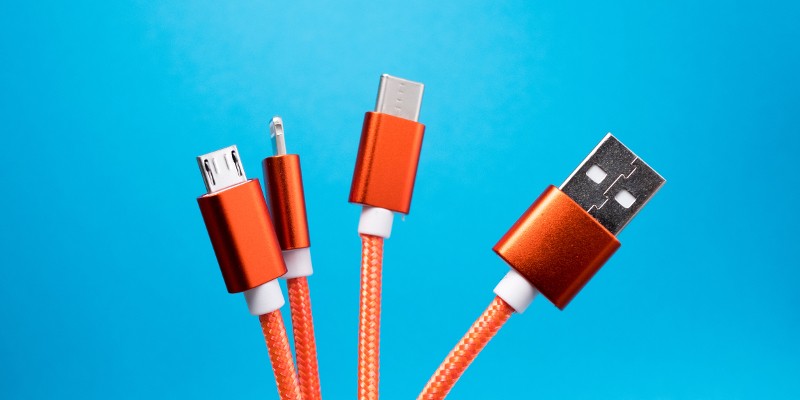
What Is Juice Jacking? Is It Safe to Use Public USB Ports?
You're in a public place, you need to use your smartphone, but you've forgotten to charge it up before you left home. You don't have a charger, and you've never really grown used to carrying bulky power banks with... Read more

Beware of the Clever "New Device Signed in to Your Stripe" Phishing Scam
As a whole, cybercriminals don’t tend to discriminate in their choice of targets. Between those who specialize in corporate extortion or prefer brutalizing small companies, government institutions, or performing DDOS... Read more
Data of More Than 600,000 Email.It Users Has Been Hacked and Sold on the Dark Web
Data breaches have been a constant plague on the IT industry for a long time now. It seems that there's not a week that passes without news of another critical one being reported by a major company, such as Equifax or... Read more

Hijacked Routers Used to Spread Coronavirus Malware-Ridden Apps
We are living through a pandemic, and in this time of unrest, panic surrounding Coronavirus has yet to subside. People feel uneasy and scared of what's to come. In these frightening times, cybercriminals thrive.... Read more

'I Got Phished' Promises to Notify the Victims of Phishing Scams
If most of your work tasks are performed online, you probably encounter phishing emails from time to time. Everyone knows (at least in theory) that they need to avoid phishing, but sometimes it is hard to tell... Read more
Rainbow Table Password Attack - What Is It and How Do You Protect Yourself From It
A rainbow table is just one of the many potent tools in the arsenal of the cybercriminals of today. While a rainbow table password attack has its limitations, it does give hackers the opportunity to effectively steal... Read more

$405 Million Has Been Stolen From Military Veterans Using Scams Since 2012
When it comes to fraudsters, they feel no shame as they prey on the most vulnerable people like military veterans who, for example, might require money or might be unable to say no to other soldiers in need. According... Read more

What Is Disk Image and How You Can Use It
Optical disks are not really relevant these days – indeed, many people consider them something of a relic of a bygone age. It’s fair to say that optical disk drives were a significant evolutionary step in a... Read more
Which Two-Factor Authentication Option Is the Best?
On the face of it, two-factor authentication (2FA) is a ruthlessly simple and incredibly effective security feature. In essence, by implementing two-factor authentication, you ensure that an attacker can't take over a... Read more

Downloading Pirated Software Is Not Only Illegal but Also Dangerous
Where do you go when you want to install a new program or a new game? Hopefully, you are relying on legitimate download websites and you are doing your research before committing to anything. Note that if you end up... Read more

1 Billion WI-Fi Connected Devices Are Vulnerable Due to a Security Vulnerability
IoT is the future, or so we're being told all the time - with technology not so much marching, but rather frog leaping into orbit, smart homes and interconnected appliances that you can command at will from your phone... Read more
Scam Alert - Watch out for Fake Walmart Password Reset Email
Nowadays, technology does not so much march forward as skyrockets into new and unexpected directions at a staggering speed. Using the Internet is practically a necessity for business and personal matters.... Read more

Have You Reached Full Gmail Potential? A "Good Enough" Password Won't Do the Trick
If you don’t have a Gmail account, you must be very independent and self-sufficient. Or perhaps you’ve been living in a taiga all this time. Either way, it is a lot more common to have several Gmail accounts these... Read more