How to Backup Skype Chat History or Business Conversations
Over the years, Skype has proven to be one of the most effective communication platforms on the Internet. Launched more than 15 years ago, back in 2003, it has registered steady growth ever since it took off, and has... Read more

Do Not Fall for Fake Instagram Helper Apps That Can Steal Your Password
Why are social networks so successful? Well, in short, they are thriving because people spend quite a lot of time using them. And people do this because they're interested in what the rest of the world thinks about... Read more

There's a Fake Google Wallet App, and It Is Used to Hijack Google Accounts
You could argue that Google is the classic Silicon Valley success story. What started off as a useful search engine is now a commanding part of almost everything we do online. Over the years, Google released apps and... Read more
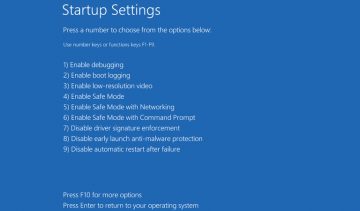
How to Fix 'Windows 10 Safe Mode Won’t Accept Password' Issue
Windows Safe mode was designed as a way to get out of all manner of problems. For example, if your VGA drivers crash your system? This is especially true in Windows 10 as it has a lot of driver problems. Safe Mode... Read more

How to Password Protect a Compressed/Zipped Folder on Windows 10 PC
Did you know that you can encrypt a folder with a password? This has always been an indispensable feature of Windows for as long as I can remember (and I can remember Windows 95). It's a staple of the OS at this point... Read more
Steps Every Outlook User Must Take in the Wake of a Major Security Breach
Last Friday, Outlook users started receiving breach notification emails from Microsoft which, in addition to telling them that an unknown attacker has accessed some of the information in their inbox, informed them... Read more

What Is Instagram's Nasty List and What to Do If You're on It?
If you're told that you've ended up on Instagram's 'Nasty List', you'll likely want to know what the reason for this is. A 'Nasty List' sounds like a list of accounts that have done something wrong, so, especially if... Read more

What Is a Baldr Data Stealer and How to Protect Your Passwords Against It
Baldr is the name of a new family of information-stealing malware. Its authors first introduced it to cybercriminal circles in January, and about a month later, Microsoft's security team reported that they have seen... Read more

It Takes Hackers 60 Seconds to Find and Attack a Vulnerable Server
Movies and, to a certain extent, mainstream media would have us believe that organizing a cyberattack involves a lot of planning, plenty of resources, and a teenage computer geek who's in a bad mood all the time. This... Read more

How to Password-Protect a Video File on Windows & Mac
Like everyone out there I'm sure you have important videos on your PC or Mac that you don't wish anyone else to see. In that case, it's completely logical to put a password on your sensitive videos just in case... Read more

What Is a Google Security Key and How Does It Work with Your Android 7.0+ Phone?
Google's security people reckon that they know a thing or two about Two-Factor Authentication (2FA) or 2-Step Verification, as they like to call it. They think that the most secure 2FA systems are the ones based on a... Read more

99 Phishing Sites but Microsoft Did Not Leave One
A phishing website is a wonderful instrument for virtual schemers. Once a phishing website is set up, the attackers can trick gullible visitors into disclosing personal information or interacting with unreliable or... Read more