
How to Protect Ourselves from DDoS Attacks on Mobile Apps
What is a DDoS attack? DDoS is short for Distributed Denial of Service attack. It is a style of cyber-attack in which a large group of devices or computers are injected with malware. This malware acts as a network of... Read more

How to Customize Your Amazon Alexa Settings for Privacy
In this article, I will outline 8 easy-to-update settings, which will customize Amazon Alexa to make her easier to work with. Each of these updates will take no more than a 1 minute to do. Enable Brief Mode Most... Read more

Privacy of 50,000 'Get' Users Compromised Amidst a Data Breach
In May 2017, a ticketing platform by the name of Qnect made the news for all the wrong reasons. Qnect's userbase was mostly comprised of Australian students who suddenly started receiving some strange unsolicited... Read more

Millennial Money - How to Outsmart Smartphone Scammers
With online banking and payment being an integral part of the regular smart device owner’s experience nowadays, it is no wonder that cyber-criminals are now actively targeting mobile devices as a matter of course. As... Read more

Robotexts Are the Next Annoying Spam Ready to Blow up Your Phone
Is there anything more annoying than robocalls? Turns out there is. Robotext reports have been increasing even as phone carriers and regulators have been making steady progress against robocalls. Big-name companies... Read more
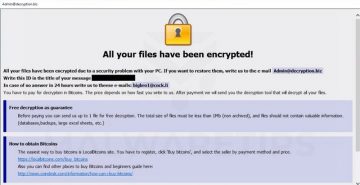
Want to Survive Ransomware - Here's How to Protect Your PC
IT security experts have argued that “ransomware is everything bad about humanity distilled into malware—maliciousness, greed, and casual incompetence”. It’s not difficult to see why some of them could hold that... Read more

Hitachi Wants to Replace Passwords with Hand Gestures
We all know that the traditional username-and-password authentication system is riddled with faults, and biometrics seems like the most obvious alternative. Unlike passwords, fingerprints and facial features are... Read more
The Customers of Foxit Software Are Warned About a Data Breach That Exposed Passwords
Foxit Software has disclosed that it was recently a victim of a security breach in which private user data was left unprotected with an unknown third party. The people whose accounts were affected have been contacted... Read more

Schemers Hide Behind SharePoint to Expose Victims to Phishing Scams
We've often said on these pages that in technical terms, phishing is the simplest form of cybercrime. Even so, pulling off a successful phishing attack still requires some preparation, especially if the crooks are... Read more

Do Not Download These Remote Apps or Your Paytm Account and Bank Account Details May Get Leaked
Paytm account owners have been warned about a new threat. The company has asked its account holders to be careful, especially if they're updating their KYC (Know Your Customer). As you can imagine this news is of... Read more

24 Google Play Apps Found to Distribute the Joker Malware
According to Google Play, the malicious apps that were designed to infect unsuspecting Android users with the new Joker malware were downloaded a total of 472,000 times. The number does seem relatively high, but we... Read more
Shenzhen i365 Tech Sells 600,000 GPS Trackers with '123456' Set as the Default Password
In August 2018, the State of California passed a bill which is supposed to make Internet of Things (IoT) devices more secure. It has already caused more than a little controversy, with some arguing that lawmakers... Read more