
Stolen Fortnite Accounts Are Making Millions for Cybercriminals
Despite the latest tensions between Epic Games and Apple, Epic's Fortnite is still a seemingly bottomless gold mine. However, the game is generating a lot of money not just for Tim Sweeny and his company but also for... Read more

Warning: Not All Zoom Invitations Can Be Trusted
With the global Covid-19 pandemic still in full swing and millions of people working from home, technology has become even more important for keeping in touch and staying connected, both with family members and with... Read more

Mobile Malware Spreading Through COVID-19 Test SMS
Cybercriminals are not letting go of the Covid-19 anxiety that is still gripping the world and are doing their best to abuse it. A brand new mobile scam that spreads malware has joined the dozens of Covid-themed... Read more

Nearly 80% of Companies Have Suffered a Cloud Data Breach in the Last 18 Months
It is only logical that businesses are migrating online, and it is only a matter of time until almost all the data and information is stored and accessed via cloud services. However, just like anything out there,... Read more

10 Essential Security Settings in Smartphones You Should Use to Protect Yourself
When was the last time you reviewed your phone’s security settings? Do you get the impression that your mobile device is a lot safer to use than your computer? Well, cybercrime evolves just as fast as everything else... Read more
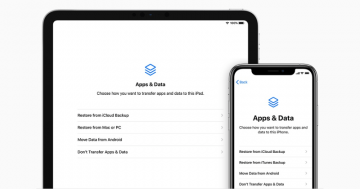
What is the Apps and Data Screen on iPhone and How to Use It
The Apps and Data screen is one of the most important menus on an iPhone that allows users to perform a number of crucial tasks with the device. You can use the Apps and Data screen to transfer ownership of the... Read more

Online Design Platform Canva Abused by Hackers for Phishing
Bad actors, especially those focusing on scams and phishing emails, have been shifting their focus on exploiting cloud services and online tools for their campaigns. After a rise in phishing emails using content... Read more

Schemers Use Pretexting and Vishing to Gather Passwords and Sensitive Data
How difficult is it to trick someone into revealing sensitive data like passwords over phone calls, text messages, or emails? Sadly, it is easier than you might think as hackers employ phishing techniques like... Read more
How to Set up a Picture Password on Windows 10?
Modern technology allows for a large number of ways to protect your logins on all devices. Different people have different preferences about how they want to access their computers and phones, ranging from thumbprints... Read more

Thousands of Players Upset After Michigan Lottery Password Reset
Some lottery players in Michigan were disgruntled to find their accounts inaccessible after the state lottery pushed a site update in mid-August 2020. The website of the lottery implemented a new security update on... Read more

Tech Company Garmin Pays Millions After Ransomware Attack
Garmin, a brand associated with a lot of different GPS systems and sports equipment, reportedly paid millions of dollars of ransom after hackers infected its systems with ransomware in late July 2020. According to... Read more

3 Types of Complicated and Costly Email Threats That Organizations Should Watch Out For
It is estimated that $2.9 million is lost to cybercrime every single minute and that large companies are losing $25/minute on security breaches alone. These are shocking numbers, and it is likely that they will grow... Read more